As part of the IT department’s campaign to keep online accounts safe, students and faculty are required to sign up for multi-factor authentication (MFA) by Nov. 18. MFA enhances an account’s security by confirming an individual’s identity through another factor, such as texts or calls.
Faaress Parham, IT security architect, said that a total of 46 accounts have been compromised since mid-September.
“They are almost at one a day,” Faaress said. “It does come in waves. Sometimes there will be a week where there are none, and then there will be one day where there are 17.”
While Faaress said that 46 breaches per month are within Rollins’s norm, he would ideally like the number to drop to zero. He said that encouraging everyone with a Rollins email account to sign up for MFA is crucial to IT’s campaign for a safer online campus.
However, “empowering members in higher education to sign up for MFA is difficult,” Faaress said, especially when coordinating a diverse group of people who own a variety of technologies.
“We have multiple ways to get them to authenticate, but the big hurdle we have is trying to level the playing field with security and academic freedom,” Faaress said. “We certainly don’t want to impose things on users, but there is a line to also keep the campus safe.”
The largest cause of compromised accounts at Rollins is phishing, which occurs when an attacker impersonates a person or service via email. The attacker will make a suspicious claim to lure information from the user.
One of the first signs of compromise occurs when several suspicious emails leave a user’s outbox, or a folder for outgoing mail, and the user’s account becomes a spreader of phishing attacks.
“Rollins College is a target,” Faaress said. “People want to steal money; they want to steal our research. From the campaigns that I’ve seen, they’re very specifically targeted to certain students or populations or groups.”
When an account is compromised, IT receives an alert that the account was accessed from another country within an impossibly short time frame. IT then locks the account for safety and notifies employees at the Help Desk, who contact the user, verify their identity, and offer solutions to protect the account.
Faaress said that many attacks targeting Rollins originate from Nigeria, but other attackers intentionally make their locations unknown.
The vulnerability of personal data within a compromised account can lead to serious consequences such as identity theft and defamation. College-level data breaches can lead to institutional shutdowns, which occurred at Howard University last month.
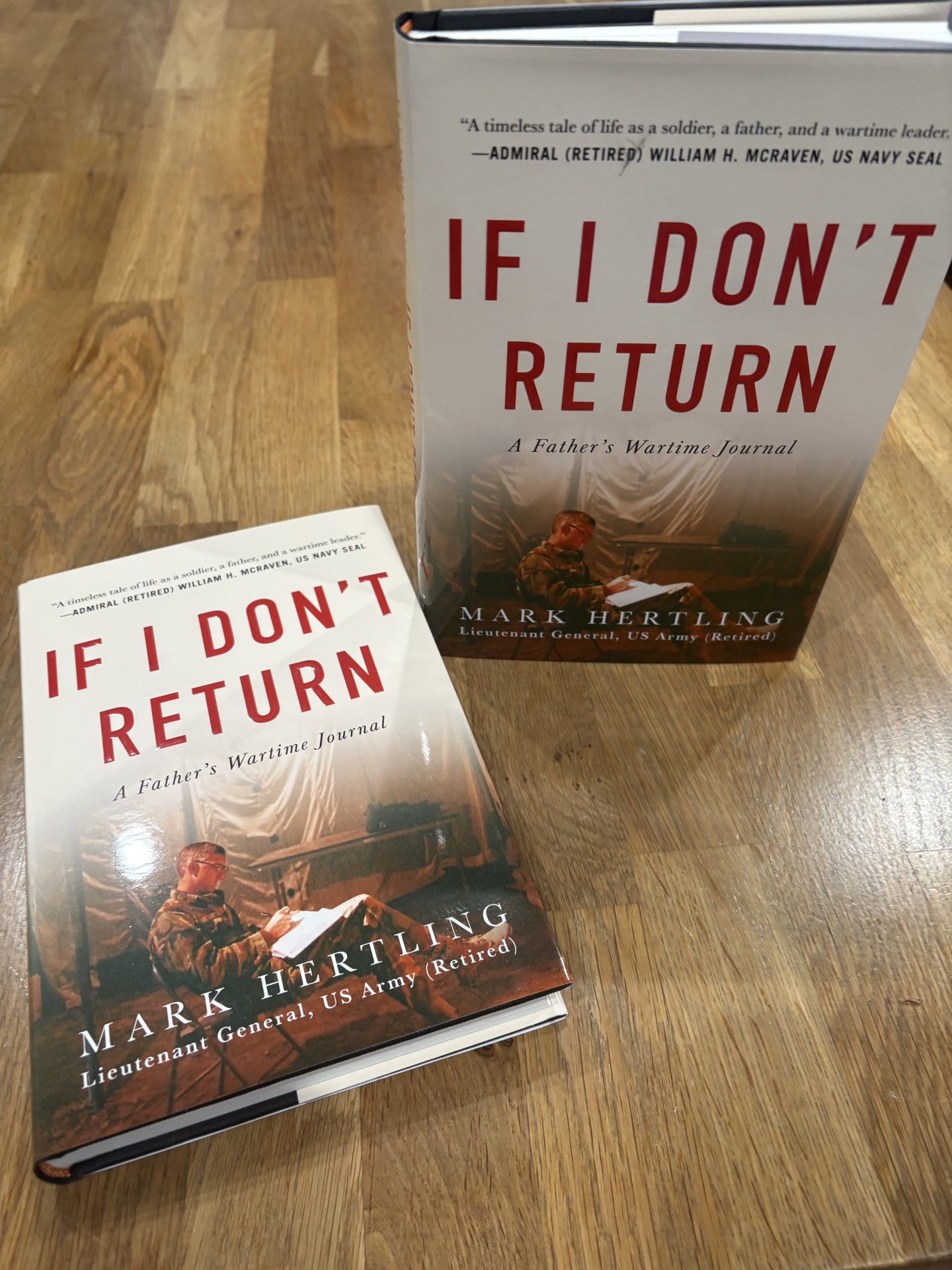
In 2019, a Rollins phishing scam targeted Dr. Justin Paul, visiting professor of International Business and Marketing. The attacker impersonated Chair of the Department of Business Dr. Timothy Pett and attempted to steal $700 worth of iTunes gift cards from Paul.
“It can get bad very quickly,” Faaress said. “Usually, people don’t look at this until something bad happens. We have always been in a reactive state when it comes to cyber security […] We are trying to be more proactive.”
According to Cyber Security Dive, ransomware attacks, or viruses that target personal data and threaten to block it or publish it, increased 100 percent on college campuses from 2019 to 2020. On average that year, the attacks cost institutions $447,000.
Following Phishing Awareness Month in October, Faaress said that the IT team deliberately chose Nov. 18 as the deadline for student and faculty MFA authentication.
“We wanted to select a date where we could have the most support for users,” Faaress said. “[…] We don’t want users to come back to campus for their spring semester and all of the sudden they see something that wasn’t communicated with them.”
MFA is just one way Faaress hopes Rollins can be proactive when it comes to cyber security. IT has implemented a report feature in Outlook, in which users can indicate if they think an email is spam or phishing. If the user tags an email as phishing, IT is alerted.
“We can look at it and take action,” Faaress said. “If there is an internal phishing campaign, or external, and if enough users report it, it will take action on its own. This is how we try to instill a culture of security.”
Users can proactively self-enroll for MFA authentication here before Nov. 18. If faculty and students do not enroll by the deadline, then MFA will be automatically applied to their account, according to a campus-wide email sent by President Grant Cornwell.
“Most colleges and universities do not require an MFA. We would actually be a leader in higher ed if we could implement this in all accounts,” Faaress said. “I know I’m the security person for the college, but in reality, everyone’s a security person here.”








[…] while on campus. However, the presence of cyber attacks is closer than we think. In an article written by The Sandspur in November, it was indicated that approximately 45 data breaches per month were within Rollins’s […]
[…] Use Multi-Factor Authentication (MFA). Although this can be a tedious step in your login processes, you will essentially use MFA to add an extra level of verification that attackers cannot obtain. […]